As September quickly approaches and schools are back in session for the fall semester, it’s a reminder that audit season for Advanticom’s ISO 27001 certification is quickly kicking into full gear. This fall, Advanticom will be completing our sixth full year of ISO audits and with the start of 2023 we will be kicking off our third successive three-year ISO 27001 compliance cycle. It is humbling to reflect upon what Advanticom’s alignment to this framework has done for the maturity of our organization and Information Management Security System (ISMS) over the years. We have both our internal and external auditing partners to thank for pushing us year over year for continual service improvements across our ISMS.
In addition to maintaining our own ISO 27001 certification, Advanticom has helped many organizations implement specific portions of the ISO 27001 framework to enhance the security posture of their businesses. We have engaged with clients to help establish Security Incident Response Plans, and Business Continuity Plans. We have instituted ISO policies and procedures across many domains of Information Security for our clients. Organizations of all sizes can benefit from the various standards covered within ISO 27001 Information Security without making the full commitment of achieving the ISO 27001 certification themselves. This is a unique set of services that Advanticom is pleased to offer to our clients. We are always happy to share our unique expertise in the world of Information Security.
Curious about what ISO 27001 is?

ISO framework and the purpose of ISO 27001
The ISO framework is a combination of policies and processes for organizations to use for alignment to a best practice framework. ISO 27001 provides this structure to help organizations, of any size or any industry, implement, operate, monitor, review, maintain and continually improve their information security management systems. ISO 27001 details the specification for Information Security Management System (ISMS) to help organizations address people, processes, and technology about data security to protect the confidentiality, integrity, and availability of their information assets. The ISO 27001 framework is based on risk assessment and risk management, and compliance involves identifying information security risks and implementing appropriate security controls to mitigate them.
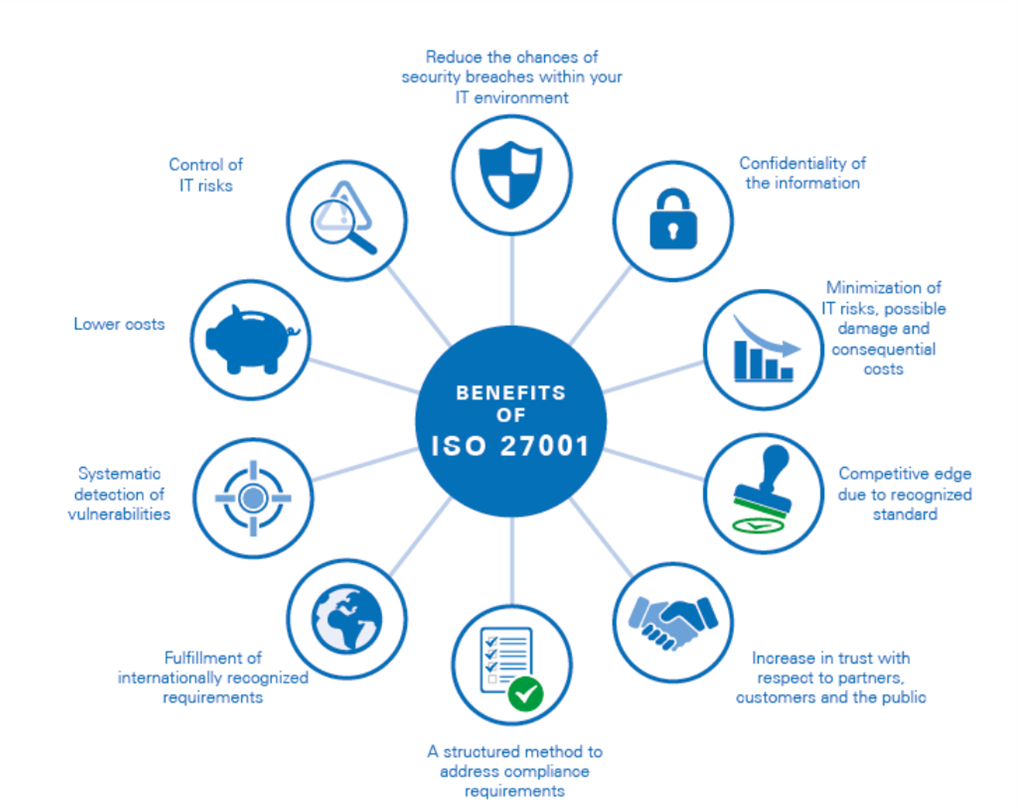
Why is ISO 27001 important?
Not only does the standard provide companies with the necessary know-how for protecting their most valuable information, but a company can also get certified against ISO 27001 and, in this way, prove to its customers and partners that it safeguards their data. Because it is an international standard, ISO 27001 is easily recognized all around the world, increasing business opportunities for organizations and professionals.
What are the 3 ISMS security objectives?
The goal of ISO 27001 is to protect three aspects of information:
- Confidentiality: only the authorized persons have the right to access information.
- Integrity: only the authorized persons can change the information.
- Availability: the information must be accessible to authorized persons whenever it is needed.
What is an Information Security Management System (ISMS)?
An ISMS is a set of rules that a company needs to establish to:
- Identify stakeholders and their expectations of the company in terms of information security
- Identify which risks exist for the information
- Define controls (safeguards) and other mitigation methods to meet the identified expectations and handle risks
- Set clear objectives on what needs to be achieved with information security
- Implement all the controls and other risk treatment methods
- Continuously measure if the implemented controls perform as expected
- Make continuous improvement to make the whole ISMS work better
This set of rules can be written down in the form of policies, procedures, and other types of documents, or it can be in the form of established processes and technologies that are not documented. ISO 27001 defines which documents are required, i.e., which must exist at a minimum.
What are the 14 domains of ISO 27001?
There are 14 “domains” listed in Annex A of ISO 27001, organized in sections A.5 to A.18. The sections cover the following:

- Information security policies: The controls in this section describe how to handle information security policies.
- Organization of information security: The controls in this section provide the basic framework for the implementation and operation of information security by defining its internal organization (e.g., roles, responsibilities, etc.), and through the organizational aspects of information security, like project management, use of mobile devices, and teleworking.
- Human resource security: The controls in this section ensure that people who are under the organization’s control are hired, trained, and managed in a secure way; also, the principles of disciplinary action and terminating the agreements are addressed.
- Asset management: The controls in this section ensure that information security assets (e.g., information, processing devices, storage devices, etc.) are identified, that responsibilities for their security are designated, and that people know how to handle them according to predefined classification levels.
- Access control: The controls in this section limit access to information and information assets according to real business needs. The controls are for both physical and logical access.
- Cryptography: The controls in this section provide the basis for proper use of encryption solutions to protect the confidentiality, authenticity, and/or integrity of information.
- Physical and environmental security: The controls in this section prevent unauthorized access to physical areas and protect equipment and facilities from being compromised by human or natural intervention.
- Operations security: The controls in this section ensure that the IT systems, including operating systems and software, are secure and protected against data loss. Additionally, controls in this section require the means to record events and generate evidence, periodic verification of vulnerabilities, and make precautions to prevent audit activities from affecting operations.
- Communications security: The controls in this section protect the network infrastructure and services, as well as the information that travels through them.
- System acquisition, development, and maintenance: The controls in this section ensure that information security is considered when purchasing new information systems or upgrading the existing ones.
- Supplier relationships: The controls in this section ensure that outsourced activities performed by suppliers and partners also use appropriate information security controls, and they describe how to monitor third-party security performance.
- Information security incident management: The controls in this section provide a framework to ensure the proper communication and handling of security events and incidents, so that they can be resolved in a timely manner; they also define how to preserve evidence, as well as how to learn from incidents to prevent their recurrence.
- Information security aspects of business continuity management: The controls in this section ensure the continuity of information security management during disruptions, and the availability of information systems.
- Compliance: The controls in this section provide a framework to prevent legal, statutory, regulatory, and contractual breaches, and audit whether information security is implemented and is effective according to the defined policies, procedures, and requirements of the ISO 27001 standard.
Interested in learning more? Reach out to Advanticom for a discussion around how your organization can benefit from alignment to the ISO 27001 framework.