In the world of IT and cybersecurity, it’s one thing to talk about security.It’s quite another to live it—day in, day out, year after year—under rigorous independent scrutiny. This year, Advanticom reaches a rare and meaningful milestone: a full decade of continuous alignment with the ISO 27001 international standard for information security management. As we….

From Adoption to Oversight: Why AI Needs SIEM Monitoring
Artificial Intelligence tools like Microsoft Copilot, ChatGPT, and Google Gemini are transforming how employees do their work. AI models promise huge efficiency gains, from drafting documents to analyzing data, but like any new technology these tools also introduce new security challenges for organizations to manage. For business leaders, the key question isn’t if you should….

Co-Managed IT Services Yields Improved Cybersecurity Protections
Co-managed IT services provide enhanced cybersecurity outcomes by combining the strengths of your internal IT team with the expertise and resources of an external third-party service provider. This hybrid approach enables 24/7 live coverage, access to specialized cybersecurity expertise, and more reliable IT systems. In today’s complex threat landscape, co-managed IT is the optimal solution….

Strengthening Corporate Security with Multi-Factor Authentication & Password Managers
Every organization has countless passwords (keys) to access their corporate network. Each employee manages passwords for various systems like email, VPN, ERP, CRM, and HR. Executives and accountants often have even more to protect, accounting and financial systems, banking information, and maybe even proprietary data or trade secrets. Unfortunately, many companies have terrible password practices….
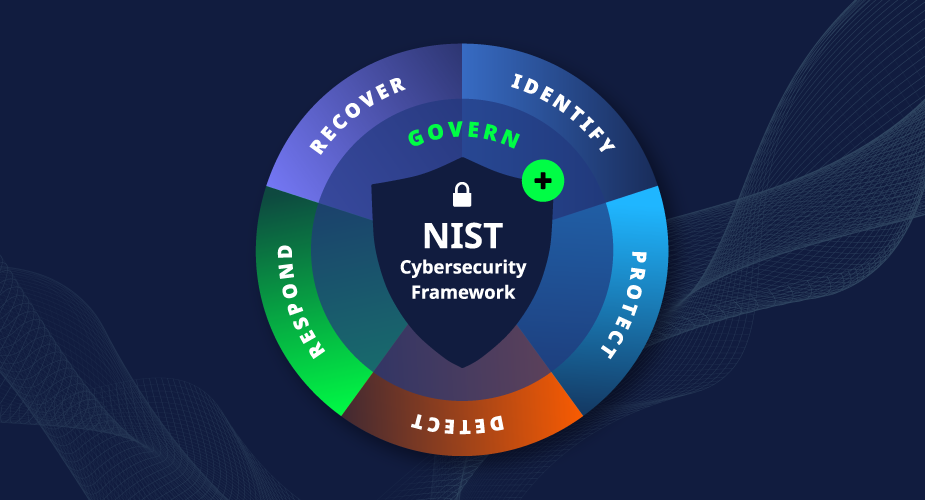
Improve Cyber Hygiene in 2024: Make A New Year’s Resolution to align with NIST Cybersecurity Framework
2024 is a great time for business owners and executives to be aware of the investments that the federal government has made to help businesses with cybersecurity best practice initiatives. For those not paying close attention there is a particular organization – the National Institute of Standards and Technology (NIST). NIST first produced their Cybersecurity….